Fortinet Philippines recently held its Security Summit 2021 via a livestream event together with the media to share some key updates on the following agenda/topics: IDC’s report and findings; market trend and threat intelligence; and making security at the core of digital success.
Present during the virtual event are Fortinet representatives: Louie Castañeda, Country Manager; Jonas Walker, Security Strategist and Napoleon Castillo, Manager of Systems Engineering.

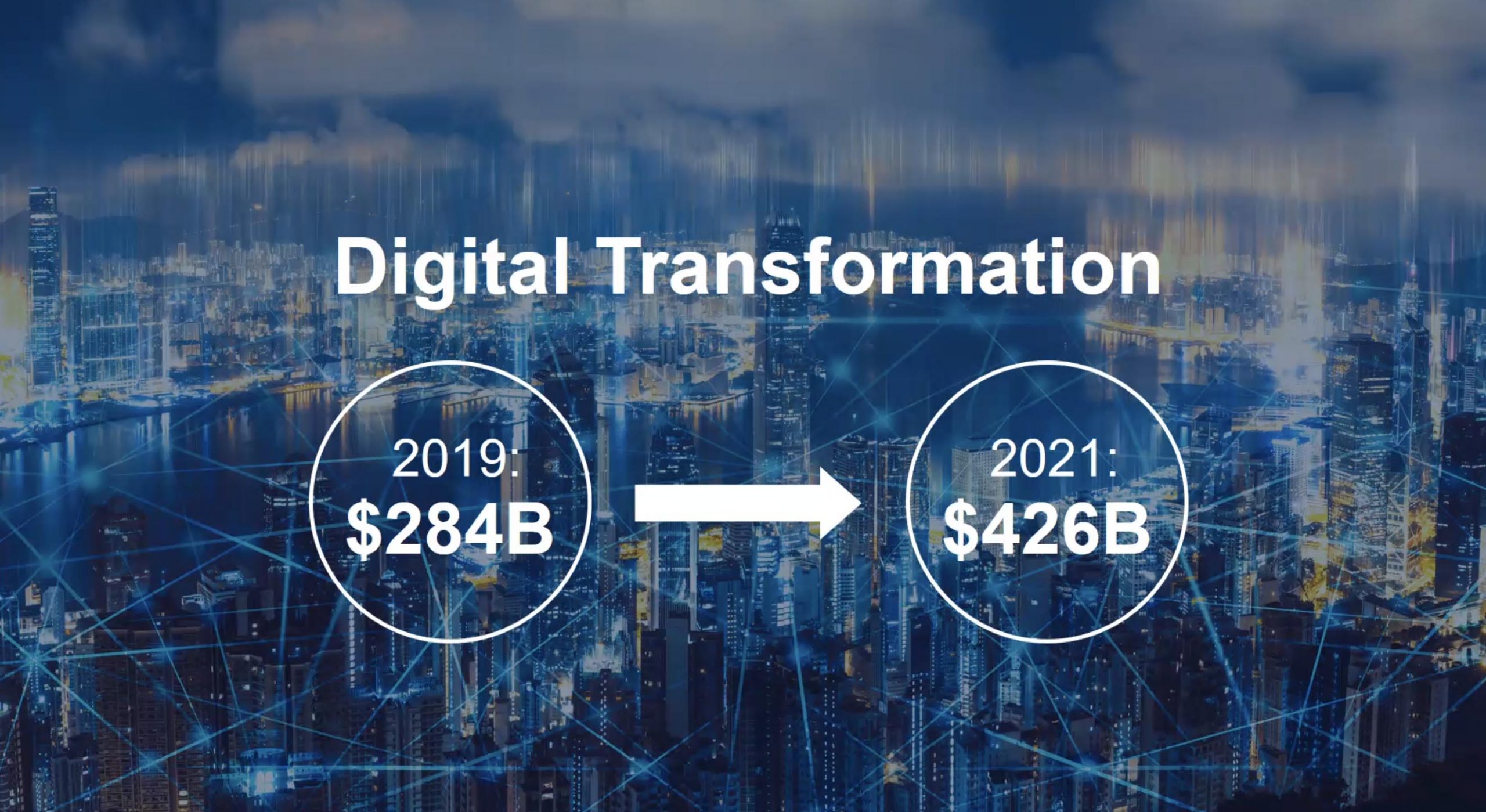
Organizations across Asia Pacific that adapted quickly to the pandemic by accelerating their digital transformation could have their hard-won resiliency threatened due to misalignment between business priorities and technology strategies, but a holistic, carefully-aligned security approach and the right partnerships would help them retain their resiliency gains.
A new InfoBrief by IDC, a leading provider of global IT research and advice, spotlights this imperative and reality, reinforcing the commitment by cybersecurity leader Fortinet® to helping CISOs and their security teams remain relevant in a digital-first world.
Sponsored by Fortinet, the IDC InfoBrief: Stop Reacting, Start Strategizing (August 2021 IDC Doc #AP241253IB) outlines the unique trends, risks and challenges for businesses in six economies across the region alongside a pattern of mismatched business and technology concerns.
Paradox of Misaligned Priorities
According to IDC’s research, CxOs cited building resilience/mitigating risk (61%) and cost reduction/optimization (63%) as top business priorities. For technology teams, both IT security investments and a shift to hybrid cloud models have been proven to address the risk issues of continuity and security. Yet, IDC has found that implementing security technologies to reduce risk (33%) is one of the lowest ranked technology priorities.
CISOs in all markets are challenged with recruiting talent which is critical to the success of IT security teams. In contrast, improving the ability to attract and retain the workforce was seventh in terms of C-suite business priorities for 2021.
Within this paradox of misaligned priorities, CISOs and cybersecurity strategies must evolve to complement the business and achieve true resiliency.
“Keeping the business safe even as cybersecurity threats escalate and the organization’s attack surface expands remains the core concern of the CISO. But to ensure that their team makes a positive contribution to the overall business, tech leaders now need to also align their security strategies with other C-suite priorities, like optimizing costs, enabling business growth, and improving business resilience,” said Louie Castañeda, country manager, Fortinet Philippines. “Stymied by the misalignment of C-suite priorities and recruitment concerns, CISOs that work with the right partners will be best able to devise the cybersecurity strategy holistically and execute a successful cybersecurity program.”
Threat Landscape
Accordingly to IDC, the Philippines’ top risk concerns are existing corporate network (40%) and around integration with existing operational technology (36%).
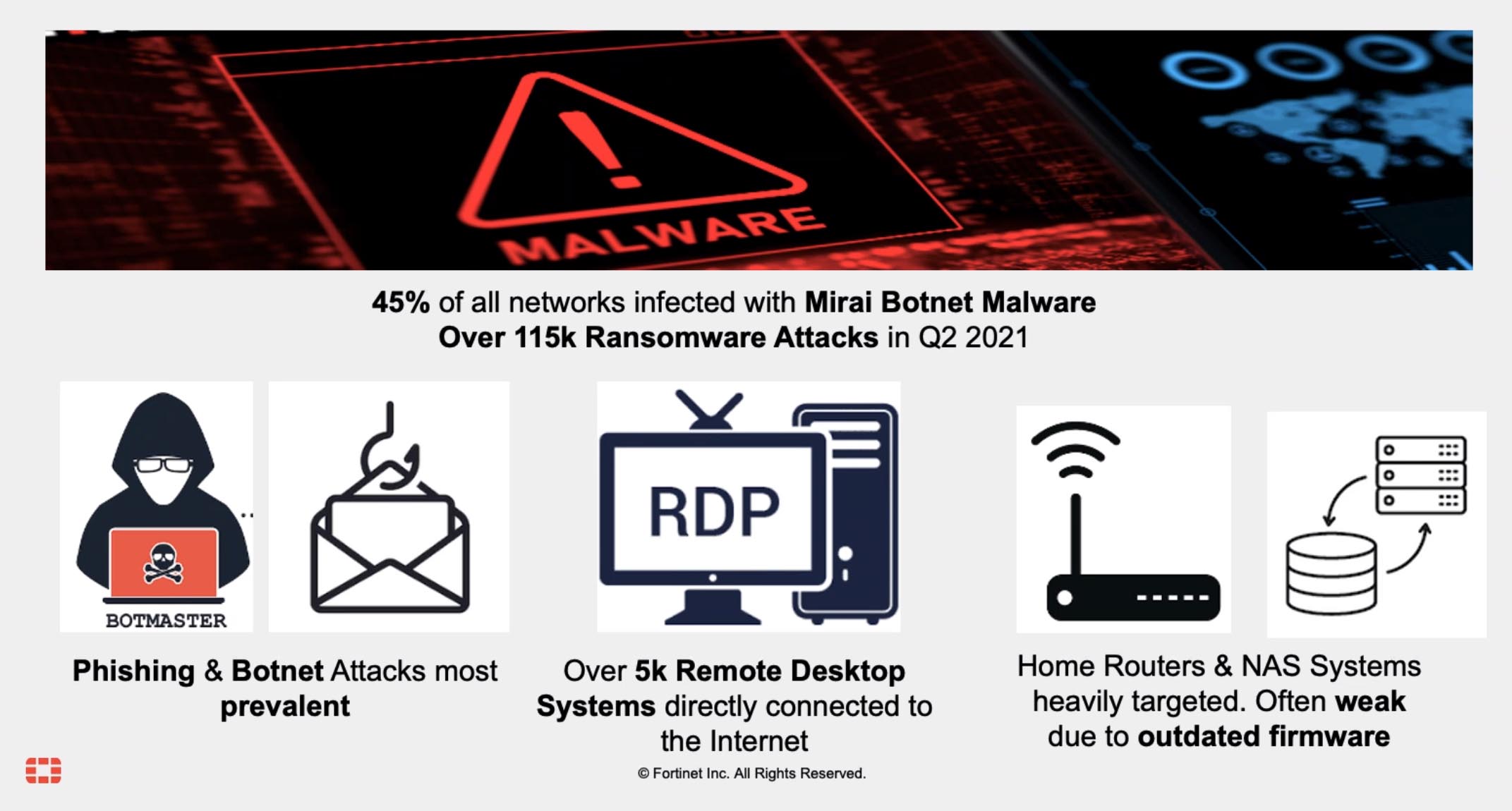
In addition, the latest FortiGuard Labs Global Threat Landscape Report from the first half of 2021 demonstrates a significant increase in the volume and sophistication of attacks targeting individuals, organizations, and increasingly critical infrastructure. The expanding attack surface of hybrid workers and learners, in and out of the traditional network, continues to be a target.
Locally, attacks are also rising. Between January to July this year, the National Computer Emergency Response Team (NCERT) has handled 601 incidents with Malware and Malicious Files (204), Unauthorized Scanning (140), and Brute Force Attack (99) as the top three cases.
Organizations face risks and a threat landscape with attacks on all fronts. However, IDC’s Asia/Pacific Digital Resilience Scorecard revealed that only 33% of organizations in the Philippines have a robust approach to cybersecurity.

Best Practices
Taking these trends and challenges into account, organizations are urged to adopt a range of business and security strategies to ensure they can continue to operate successfully and stay resilient as IT architectures and security risks evolve at pace. The recommendations include:
- Ensure Alignment of Business and Technology Priorities and Processes: Effective security requires ongoing reinforcement from the executive level down. Organizations have to review their security strategy and make sure it is aligned with their business priorities. Employees now work from anywhere in the new normal and to secure a remote workforce, organizations must align business processes such as finance and HR with best practices around communication privacy and authentication. These processes should also align with cultural processes that promote effective communication in an agile, trust-based environment.
- Ensure Your Cybersecurity Architecture Can Support New Business Architecture: To secure a distributed workforce, organizations have to update network architectures. Data privacy, integrity, and confidentiality need to be kept top of mind and applied across the network, not just for remote workers, as business applications and workflows need to span from the endpoint to the core network to the company’s “distributed edge” in the cloud. Securing this distributed environment requires cybersecurity solutions that are both integrated and automated.
- Deploy a holistic security solution: As organizations accelerate their digital innovation, ensuring their security can keep up with today’s fast-evolving threat landscape is critical. What used to be known as the “network perimeter” is now splintered across the infrastructure due to the explosion of network edges, work from anywhere, and multi-cloud models. Organizations need a broad cybersecurity strategy, implementing a platform with end-to-end security, and a single pane of glass approach to management offering full visibility across the entire attack surface.
- Adopt a zero trust approach: To respond to increasing and evolving threats, best practices now stipulate a “trust no one, trust nothing” attitude toward network access. IT teams must move toward a zero trust approach to cybersecurity, which means all users, all devices, and all web applications from the cloud must be trusted, authenticated, and have the right amount of access privilege.
Cybersecurity industry veteran Fortinet has a broad portfolio of complementary cybersecurity solutions that enable efficient, self-healing operations and a rapid response to known and unknown threats. Its Fortinet Security Fabric brings holistic end-to-end security to organizations of all sizes to enable broad visibility, seamless integration and automation across the entire digital attack surface and lifecycle, with converged networking and security across edges, clouds, endpoints and users.
The IDC InfoBrief: Stop Reacting, Start Strategizing report drew on the findings of various recent IDC surveys, including the IDC Asia/Pacific CxO Study, February 2021, IDC’s Global IT Skills Survey, April 2021, and IDC’s Asia/Pacific Digital Resiliency Scorecard, March 2021.

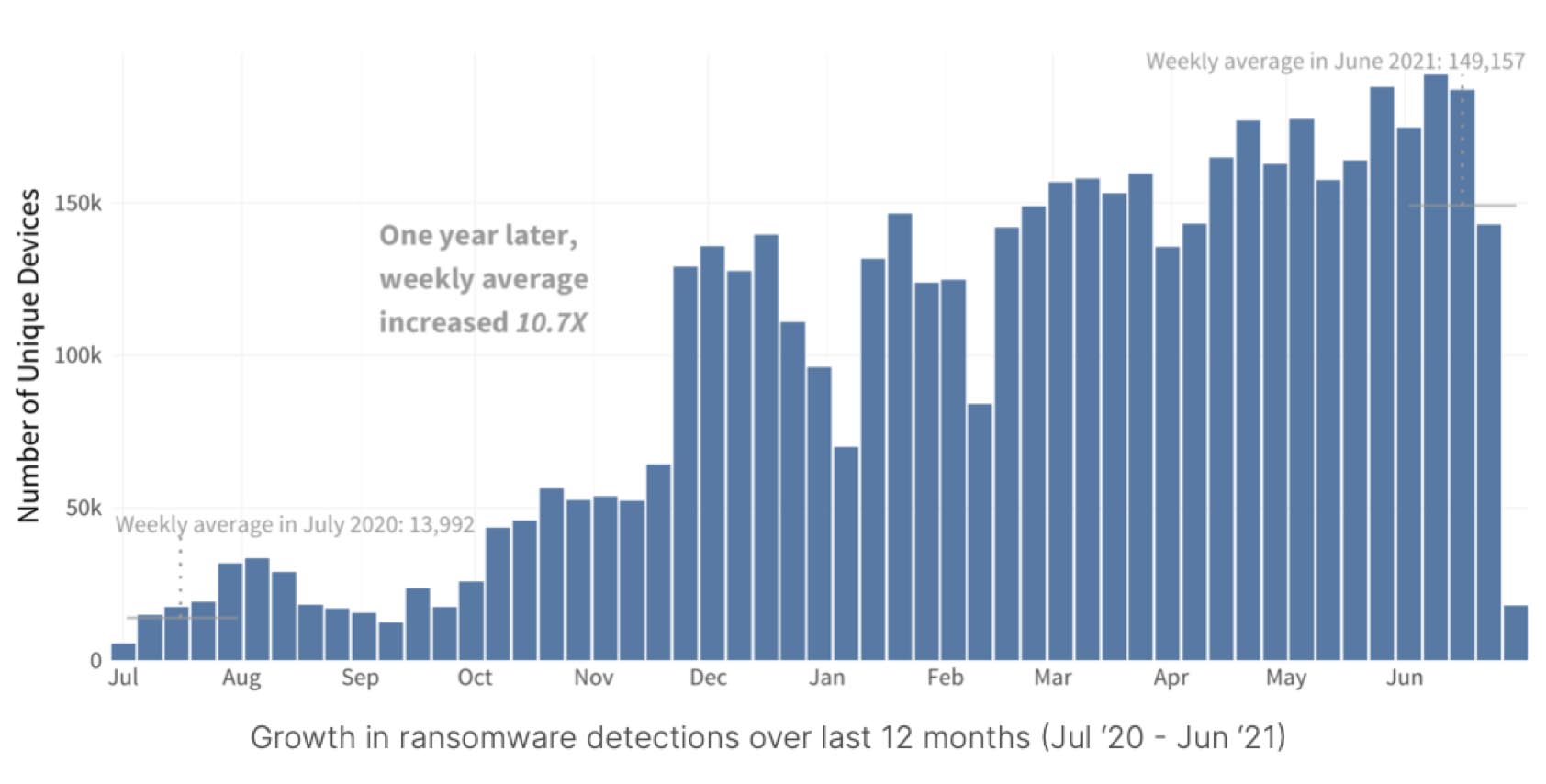
FortiGuard Labs Reports Tenfold Increase in Ransomware
Fortinet announced the latest semiannual FortiGuard Labs Global Threat Landscape Report. Threat intelligence from the first half of 2021 demonstrates a significant increase in the volume and sophistication of attacks targeting individuals, organizations, and increasingly critical infrastructure. The expanding attack surface of hybrid workers and learners, in and out of the traditional network, continues to be a target. Timely collaboration and partnership momentum across law enforcement as well as public and private sectors is an opportunity to disrupt the cybercriminal ecosystem going into the second half of 2021. For a detailed view of the report, as well as some important takeaways, read the blog. Highlights of the 1H 2021 report follow:
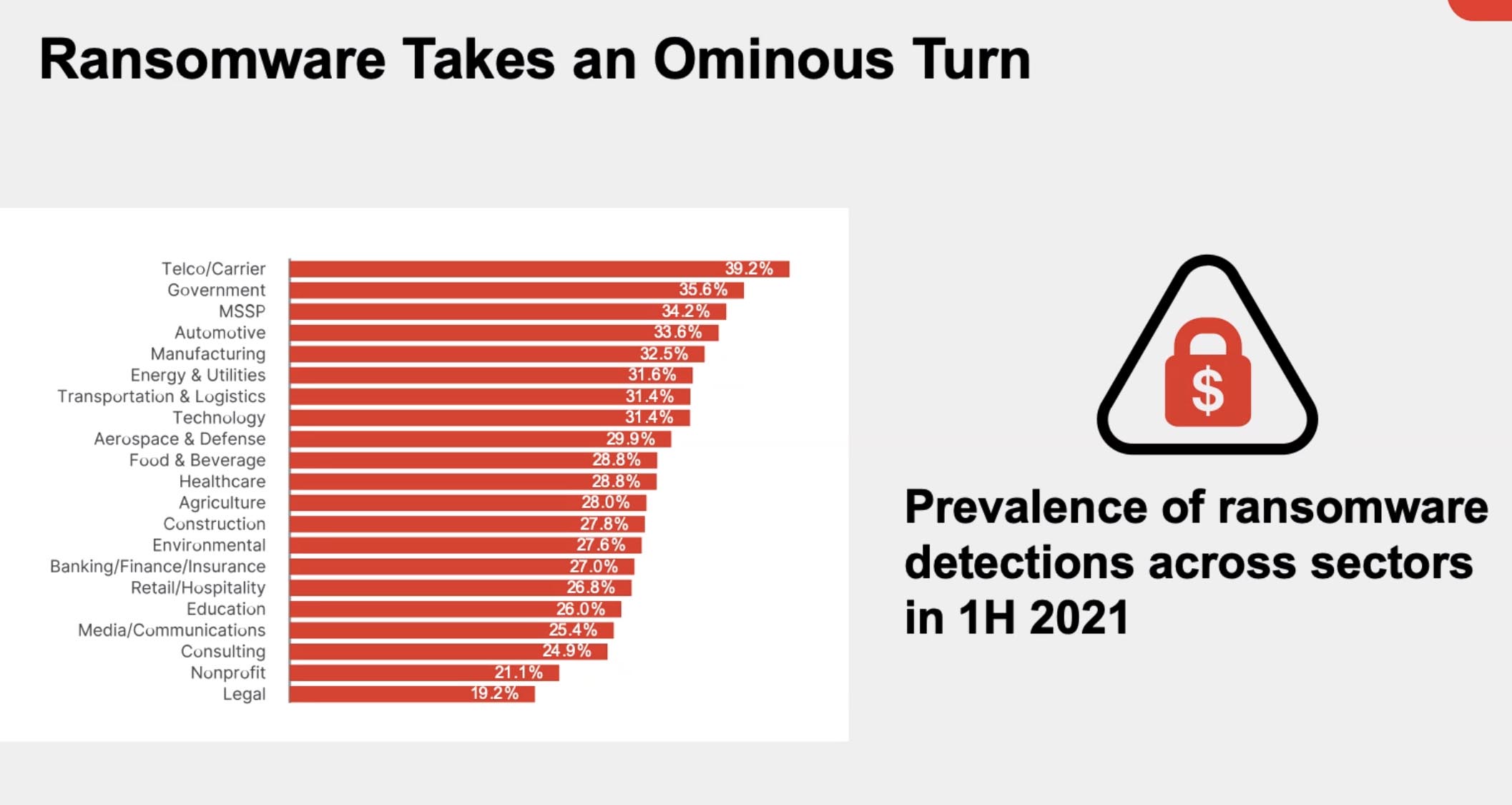
1) Ransomware Is About Much More Than Just Money: FortiGuard Labs data shows average weekly ransomware activity in June 2021 was more than tenfold higher than levels from one year ago. This demonstrates a consistent and overall steady increase over a year period. Attacks crippled the supply chains of multiple organizations, in particular sectors of critical importance, and impacted daily life, productivity, and commerce more than ever before. Organizations in the telecommunications sector were the most heavily targeted followed by government, managed security service providers, automotive, and manufacturing sectors. In addition, some ransomware operators shifted their strategy away from email-initiated payloads to focusing on gaining and selling initial access into corporate networks further showing the continued evolution of Ransomware-as-a-Service (RaaS) fueling cybercrime. A key takeaway is that ransomware remains a clear and present danger for all organizations regardless of industry or size. Organizations need to take a proactive approach with real-time endpoint protection, detection, and automated response solutions to secure environments along with a zero-trust access approach, network segmentation, and encryption.
2) One in Four Organizations Detected Malvertising: Ranking the prevalence of top malware detections by malware families shows a rise in deceptive social engineering malvertising and scareware. More than one in four organizations detected malvertising or scareware attempts with Cryxos being a notable family. Although, a large volume of the detections are likely combined with other similar JavaScript campaigns that would be considered malvertising. The hybrid work reality has undoubtedly encouraged this trend in tactics by cybercriminals as they attempt to exploit it, aiming for not just a scare but also extortion. Increased cybersecurity awareness is important as ever to provide timely training and education to help avoid falling victim to scareware and malvertising tactics.
3) Botnet Trends Show Attackers Push to the Edge: Tracking the prevalence of botnet detections showed a surge in activity. At the beginning of the year, 35% of organizations detected botnet activity of one sort or another, and six months later it was 51%. A large bump in TrickBot activity is responsible for the overall spike in botnet activity during June. TrickBot originally emerged on the cybercrime scene as a banking trojan but has since been developed into a sophisticated and multi-stage toolkit supporting a range of illicit activities. Mirai was the most prevalent overall; it overtook Gh0st in early 2020 and has reigned ever since well into 2021. Mirai has continued adding new cyberweapons to its arsenal, but it is likely that Mirai’s dominance at least still partially stems from criminals seeking to exploit Internet-of-Things (IoT) devices used by work-from-home or learning-from-home individuals. Gh0st is also noticeably active, which is a remote access botnet that allows attackers to take full control of the infected system, capture live webcam and microphone feeds, or download files. More than a year into remote work and learning shifts, cyber adversaries continue to target our evolving daily habits to exploit the opportunity. To protect networks and applications, organizations need?zero-trust access?approaches to provide least access privileges to secure against IoT endpoint and devices entering the network.
4) Disruption of Cybercrime Shows Reduced Threat Volumes: In cybersecurity not every action has an immediate or lasting effect, but several events in 2021 show positive developments specifically for defenders. The original developer of TrickBot was arraigned on multiple charges in June. Also, the coordinated takedown of Emotet, one of the most prolific malware operations in recent history, as well as actions to disrupt the Egregor, NetWalker, and Cl0p ransomware operations represent significant momentum by cyber defenders, including global governments and law enforcement to curb cybercrime. In addition, the level of attention that some attacks garnered spooked a few ransomware operators to announce they were ceasing operations. FortiGuard Labs’ data showed a slowdown of threat activity following the Emotet takedown. Activity related to TrickBot and Ryuk variants persisted after the Emotet botnet was taken offline, but it was at a reduced volume. This is a reminder of how hard it is to eradicate cyberthreats or adversary supply chains immediately, but these events are important achievements regardless.
5) Defensive Evasion and Privilege Escalation Techniques Favored by Cybercriminals: Studying higher resolution threat intelligence reveals valuable takeaways about how attack techniques are evolving currently. FortiGuard Labs analyzed the specific functionality inherent to detected malware by detonating the samples to observe what the intended outcome was for cyber adversaries. The result was a list of negative things malware would have accomplished if the attack payloads had been executed in target environments. This shows cyber adversaries sought to escalate privileges, evade defenses, move laterally across internal systems, and exfiltrate compromised data, among other techniques. For example, 55% of observed privilege escalation functionality leveraged hooking and 40% utilized process injection. A takeaway is that there is an obvious focus on defense evasion and privilege escalation tactics. Although these techniques are not novel, defenders will be better positioned to secure against future attacks, armed with this timely knowledge. Integrated and artificial intelligence (AI)-driven platform approaches, powered by actionable threat intelligence, are essential to defend across all edges and to identify and remediate shifting threats organizations face today in real time.
Partnership, Training, and AI-powered Prevention, Detection, and Response Is Vital
While government and law enforcement agencies have taken actions relative to cybercrime in the past, the first half of 2021 could be a game-changer in terms of the momentum for the future. They are working with industry vendors, threat intelligence organizations, and other global partnership organizations to combine resources and real-time threat intelligence to take direct action against cyber adversaries. Regardless, automated threat detection and AI remain essential to enable organizations to address attacks in real time and to mitigate attacks at speed and scale across all edges. In addition, cybersecurity user awareness training is as important as ever with anyone being a target of cyberattacks. Everyone needs regular instruction on best practices to keep individual employees and the organization secure.
Report Overview
This latest Global Threat Landscape Report is a view representing the collective intelligence of FortiGuard Labs, drawn from Fortinet’s vast array of sensors collecting billions of threat events observed around the world during the first half of 2021. Similar to how the MITRE ATT&CK framework classifies adversary tactics, techniques, and procedures with the first three groupings spanning reconnaissance, resource development, and initial access, the FortiGuard Labs Global Threat Landscape Report leverages this model to describe how threat actors find vulnerabilities, build malicious infrastructure, and exploit their targets. The report also covers global and regional perspectives as well.
![]()